
Beyond Bosch: Why Denso and Continental ECU Reverse Engineering Matters
Denso Continental ECU Reverse Engineering together supply engine management systems to nearly half the global vehicle fleet. Toyota, Honda, Subaru, and Mazda rely heavily on Denso ECUs, while the Volkswagen Group, BMW, Ford, and PSA (Peugeot/Citroen) use Continental units across their lineups. If you only know how to reverse engineer Bosch ECUs, you are missing a massive segment of the automotive market.
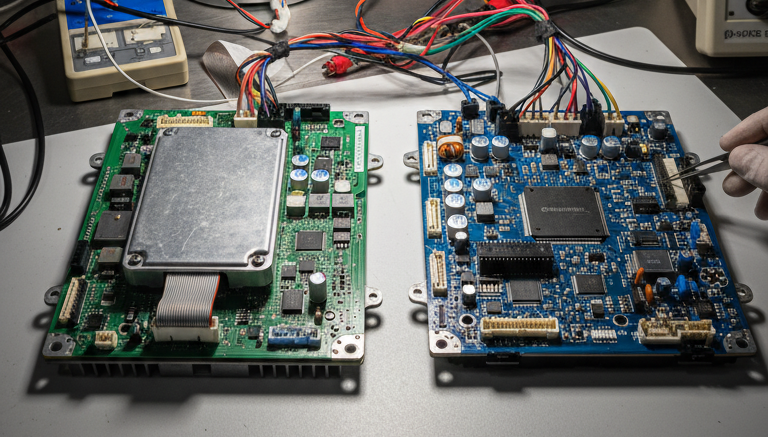
Denso and Continental ECU reverse engineering requires a different skill set than Bosch work. Different processors, different firmware architectures, different security implementations, and different extraction methods. This guide provides a comprehensive overview of both manufacturers, covering their ECU families, processor architectures, firmware extraction approaches, and analysis techniques. Whether you are a tuning professional, security researcher, or diagnostic tool developer, understanding these platforms expands your capabilities significantly.
Denso ECU Families and Vehicle Coverage
Denso Corporation, headquartered in Japan, is the world’s second-largest automotive supplier. Their ECU product line spans three generations, each built around different Renesas (formerly NEC/Hitachi) microcontrollers:
| Generation | Processor | Vehicles | Production Years |
|---|---|---|---|
| Gen1 | Renesas SH7055 (SuperH) | Toyota Corolla, Camry, Yaris (early models) | 2003-2010 |
| Gen2 | Renesas SH7058 / SH7059 | Toyota RAV4, Land Cruiser, Honda Civic, Accord | 2008-2018 |
| Gen3 | Renesas RH850 (R7F701202, R7F701216) | Toyota Supra, Camry (2019+), Subaru WRX, Mazda 3 | 2018-present |
The critical difference between Denso and Bosch ECUs is the processor family. While Bosch MED17 and EDC17 units use Infineon TriCore processors, Denso relies on the Renesas SuperH and RH850 architectures. This means different instruction sets, different debug interfaces, and different reverse engineering toolchains.
Denso ECU Architecture: Renesas SuperH and RH850
The Renesas SuperH (SH-2A core) is a 32-bit RISC processor with a compact instruction set. Gen1 and Gen2 Denso ECUs use SuperH variants with integrated flash memory ranging from 1 MB to 2 MB. The SH7058, found in Gen2 units, features 2 MB of internal flash, 64 KB of RAM, built-in CAN controllers, and a 10-bit ADC for sensor inputs.
Gen3 Denso ECUs use the Renesas RH850 family, which is a significant step up in processing power. The RH850/P1x series features a 32-bit RISC core running at up to 240 MHz, hardware security modules (HSM) for secure boot and key storage, up to 4 MB of flash memory, and integrated CAN-FD support. The RH850’s hardware security module is the biggest challenge for Denso and Continental ECU reverse engineering on modern platforms, as it implements secure boot chains that verify firmware integrity before execution.
Denso ECU Firmware Extraction
A key step in Denso and Continental ECU reverse engineering is obtaining the firmware binary. Extracting firmware from Denso ECUs requires methods specific to the Renesas processor family:
JTAG (AUD interface): Renesas processors use a variant of JTAG called AUD (Advanced User Debugger) for debug access. On Gen1 and Gen2 units, the AUD interface provides full read/write access to flash memory. The debug port is typically accessible through test pads on the ECU PCB. Tools like I/O Terminal and specialized JTAG adapters support Renesas AUD communication.
Boot mode: Renesas SH7058/59 processors support a serial boot mode activated by pulling specific pins during power-up. This mode allows reading and writing flash memory through a UART interface, bypassing the main firmware entirely. Boot mode is one of the most reliable methods for Gen2 Denso firmware extraction.
OBD/CAN-based extraction: Some Denso ECUs support firmware reading through CAN diagnostic protocols. Unlike Bosch ECUs that use standard UDS, Denso often implements proprietary diagnostic protocols based on KWP2000 or manufacturer-specific extensions. Toyota’s diagnostic protocol, for example, uses custom service IDs and security access sequences that differ from the standard UDS flow. For a detailed comparison of extraction techniques, see our ECU Firmware Extraction Methods guide.
Gen3 challenges: The RH850’s hardware security module complicates extraction significantly. Secure boot verification, encrypted flash regions, and debug port locking make Gen3 Denso ECUs among the most difficult to extract. Specialized tools like CG FC200 and newer versions of bench-mode programmers have developed workarounds for specific RH850 variants, but each sub-model may require a different approach.
Denso Firmware Analysis
Once the firmware is extracted, the analysis phase of Denso and Continental ECU reverse engineering begins. Denso firmware analysis differs from Bosch in several key ways:
Disassembly: The SuperH and RH850 instruction sets require dedicated processor modules. Ghidra supports both SuperH and RH850 architectures, making it the preferred tool for Denso firmware analysis. IDA Pro also supports SuperH but requires a separate plugin for RH850.
Code structure: Denso firmware tends to follow a more traditional embedded C code structure compared to Bosch’s model-based auto-generated code. Functions are generally smaller and more modular, making the decompiled output easier to read in many cases.
Calibration data: Denso uses a proprietary calibration data format that differs from Bosch’s map structure. Axis definitions, scaling factors, and map lookup routines follow Denso-specific patterns. Identifying the first map lookup function is key; once found, cross-references reveal the entire calibration data set.
Checksum algorithms: Denso uses different checksum and validation algorithms than Bosch. Common implementations include simple sum-based checksums for calibration regions and CRC-16 for communication integrity. Understanding these algorithms is essential for modifying calibration data without triggering validation errors. Our ECU Checksum and CRC Algorithms guide covers the principles that apply across manufacturers.
Continental ECU Families and Vehicle Coverage
Continental AG (formerly Siemens VDO) is the third-largest automotive ECU supplier globally. Their engine management portfolio includes two major product lines:
| Family | Application | Processor | Vehicles |
|---|---|---|---|
| Simos 8 / 10 | Gasoline (older) | Infineon TriCore TC1766/TC1767 | VW Golf V/VI, Audi A3/A4 |
| Simos 12 | Gasoline | Infineon TriCore TC1791 | VW Golf VII, Audi A3 (8V) |
| Simos 16 / 18 | Gasoline (MQB platform) | Infineon TriCore TC1793/TC298 | VW Golf VII/VIII, Audi A3/Q3, Skoda Octavia |
| Simos 19 | Gasoline (latest) | Infineon AURIX TC377 | VW Golf VIII, Audi Q5 (2021+) |
| SID 206 / 208 | Diesel | ST Micro SPC56x | PSA (Peugeot/Citroen), Ford diesel |
| SID 803 / 807 | Diesel | Infineon TriCore | BMW, PSA, Land Rover diesel |
A critical advantage for Denso and Continental ECU reverse engineering on Continental platforms: the Simos and SID 803/807 families use Infineon TriCore processors, the same architecture found in Bosch MED17/EDC17 units. This means TriCore reverse engineering skills, toolchains, and Ghidra configurations transfer directly between Bosch and Continental work.
Continental ECU Architecture: SBOOT and Security
Continental ECUs feature a two-stage boot process that is central to understanding their security model:
- SBOOT (Supplier Bootloader): A Continental-proprietary bootloader burned into a protected flash region. SBOOT handles manufacturing programming, repair operations, and initial hardware validation. It contains a backdoor command processor used during production and servicing.
- CBOOT (Customer Bootloader): The OEM-specific bootloader provided by the vehicle manufacturer (e.g., VW). CBOOT handles over-the-air updates, dealer programming, and UDS diagnostic communication.
- ASW (Application Software): The main engine control firmware, including all calibration data, diagnostic handlers, and control algorithms.
The SBOOT layer is particularly interesting for Denso and Continental ECU reverse engineering. Security researchers have documented that on Simos 18 units, the CRC-based boot password verification can be reversed, allowing recovery of the boot password from known CRC values. This opens the door to low-level flash operations that bypass the normal UDS security access chain.
Need help with Denso or Continental ECU analysis? Our team works across all major ECU manufacturers, including platforms that lack public documentation. Learn about our ECU reverse engineering services.
Continental ECU Firmware Extraction
On the Continental side of Denso and Continental ECU reverse engineering, extraction methods depend on the platform generation and security level:
Boot mode (TriCore BSL): Older Continental TriCore ECUs (Simos 8, 10, 12) support TriCore Bootstrap Loader access, similar to Bosch ECUs. This allows flash read/write through the TriCore debug interface. The boot password, unique per ECU, must be obtained or calculated to unlock this access.
SBOOT exploitation: On Simos 16/18, researchers have demonstrated that the SBOOT command processor can be accessed through specific CAN sequences during the boot phase. By sending precisely timed commands, it is possible to invoke SBOOT’s manufacturing mode, which provides unrestricted flash access. This technique requires detailed knowledge of the SBOOT protocol and timing requirements.
OBD/UDS extraction: Continental ECUs implement standard UDS services for firmware flashing. The SecurityAccess (0x27) seed-key mechanism must be bypassed or the algorithm reversed to unlock the programming session. Once unlocked, the ReadMemoryByAddress (0x23) service can dump firmware regions over the CAN bus.
Bench mode: Direct connection to the ECU on the bench (outside the vehicle) with controlled power supply and CAN communication. Bench mode tools like FLEX, KTMFlash, and KTag support many Continental variants, providing automated read/write procedures through combined boot mode and diagnostic approaches.
Continental Firmware Analysis
Analyzing Continental firmware shares significant overlap with Bosch analysis due to the common TriCore platform:
Ghidra compatibility: TriCore-based Continental ECUs load directly into Ghidra using the same processor modules and memory map techniques used for Bosch firmware. The PFLASH, DFLASH, and peripheral register layout follows the standard TriCore memory architecture.
SBOOT analysis: The SBOOT bootloader is a prime target for reverse engineering. It is relatively small (typically 64-128 KB) and contains the security validation routines, boot password checking, and manufacturing command handlers. Analyzing SBOOT reveals the security model and potential bypass paths.
Calibration structure: Continental uses ASAP2/A2L-compatible calibration data structures, similar to Bosch but with Continental-specific extensions. Map lookup routines, axis definitions, and scaling factors follow recognizable patterns that experienced analysts can identify quickly in the decompiled code.
Immobilizer integration: Continental ECUs, especially in the VW Group ecosystem, have tight integration between the engine ECU and the immobilizer system. The Component Security (CS) code exchange between the Simos ECU and the instrument cluster/gateway is a key area for immobilizer reverse engineering and ISN recovery on these platforms.
Comparing Bosch, Denso, and Continental: A Reverse Engineer’s Perspective
Having covered all three major manufacturers, here is a practical comparison for reverse engineers:
| Aspect | Bosch (MED17/EDC17) | Denso (Gen2/Gen3) | Continental (Simos/SID) |
|---|---|---|---|
| Primary processor | Infineon TriCore | Renesas SuperH / RH850 | Infineon TriCore (gasoline), ST Micro (some diesel) |
| Ghidra decompiler | Excellent (TriCore) | Good (SuperH, RH850) | Excellent (TriCore) |
| Code style | Model-based (ASCET/Simulink) | Traditional embedded C | Model-based, similar to Bosch |
| Diagnostic protocol | UDS (standard) | KWP2000 / proprietary | UDS (standard) |
| Security level | Moderate to high | High (Gen3 HSM) | High (SBOOT/secure boot) |
| Community resources | Extensive | Limited | Moderate (Simos wiki, GitHub) |
| Extraction difficulty | Well-documented, many tools | Moderate (Gen2), Hard (Gen3) | Moderate (Simos 8-12), Hard (Simos 18+) |
| Skill transferability | Baseline reference | Different arch, partial transfer | High overlap with Bosch (TriCore) |
The most important takeaway: if you already know Bosch TriCore reverse engineering, Continental Simos and SID analysis is a natural extension. The processor, memory layout, and debugging techniques are nearly identical. Denso work requires learning the Renesas architecture, but the methodology from our Advanced ECU Firmware Reverse Engineering Methodology applies regardless of the processor platform.
Working with a non-Bosch ECU platform? Denso, Continental, Delphi, Marelli, or any other manufacturer. Our team delivers reverse engineering results across all major ECU families. Contact us to discuss your project.
Practical Tips for Denso and Continental ECU Reverse Engineering
Build a processor reference library. Maintain Ghidra projects with annotated memory maps and register definitions for each processor family: TriCore TC1797, TC298, TC377 for Bosch and Continental; SH7058, RH850/P1x for Denso. This preparation saves hours on each new project.
Learn to identify the manufacturer from the firmware. Even without knowing the ECU model, firmware binaries contain clues: Bosch firmware typically starts with a characteristic header at 0x80000020; Denso binaries often include “DENSO” or Toyota part number strings; Continental firmware contains “CBOOT” or “SBOOT” identifiers. String searches in the first few kilobytes usually reveal the manufacturer.
Leverage CAN bus analysis. Before diving into firmware, CAN bus reverse engineering reveals the ECU’s diagnostic addressing, supported UDS services, and communication patterns. This reconnaissance phase is valuable regardless of the ECU manufacturer and often reveals the fastest path to firmware access.
Cross-reference checksum patterns. Each manufacturer uses different checksum algorithms for firmware validation. Bosch uses proprietary multi-area checksums, Denso prefers sum-based calculations, and Continental implements CRC-32 variants. Identifying the checksum algorithm early prevents wasted time on calibration modifications that fail validation.
Document everything. Non-Bosch ECU platforms have significantly less community documentation. Every finding you document, from memory maps and register definitions to function identifications and checksum algorithms, builds a knowledge base that accelerates future projects.
Let's Work Together
Need Professional Assistance with Reverse Engineering or Cybersecurity Solutions? Our Team is Ready To Help You Tackle Complex Technical Challenges.