What Is an ECU Immobilizer and Why Does It Matter?
An ECU immobilizer is an electronic security system embedded in modern vehicles that prevents the engine from starting without the correct transponder key. Unlike a simple mechanical lock, this system relies on cryptographic authentication between multiple electronic modules. When the immobilizer fails, gets corrupted, or needs to be bypassed for legitimate ECU replacement, reverse engineering becomes the only reliable solution.
Every modern vehicle manufactured after the late 1990s contains some form of ECU immobilizer. The system ties the engine control unit to a specific set of transponder keys through encrypted serial numbers, challenge-response algorithms, and in many cases, rolling codes. Understanding how these anti-theft systems work at a deep technical level is essential for ECU replacement, key recovery, forensic analysis, and security research.
This guide covers the complete technical landscape of ECU immobilizer reverse engineering: from authentication protocols and EEPROM data structures to ISN recovery techniques and practical cloning workflows.
How ECU Immobilizer Authentication Works
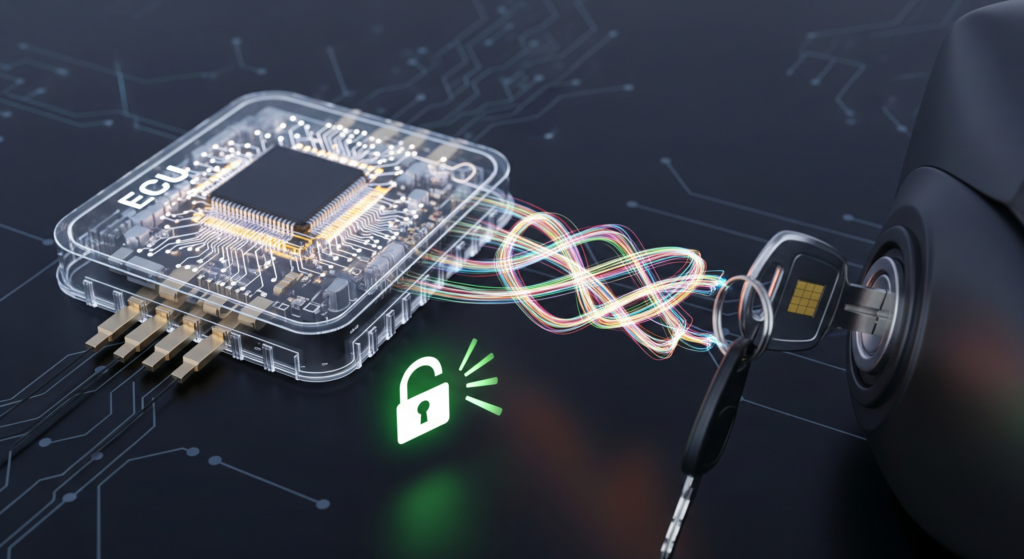
The core principle behind every ECU immobilizer is challenge-response authentication. When you insert a key or press the start button, the following sequence occurs in milliseconds:
- Antenna excitation: A ring antenna around the ignition barrel (or near the start button) sends a low-frequency RF signal to power the passive transponder chip inside the key.
- Transponder response: The transponder chip wakes up and transmits its stored identification data back to the antenna coil.
- Challenge generation: The immobilizer module (or the ECU itself, depending on architecture) generates a random challenge value and sends it to the transponder.
- Cryptographic computation: The transponder uses its internal secret key to compute a response based on the challenge. The immobilizer module performs the same computation independently.
- Response verification: If both computed values match, the system authorizes fuel injection and ignition. If they do not match, the engine cranks but will not start.
This challenge-response mechanism ensures that simply copying the transponder’s static ID is not enough to defeat the immobilizer. The secret key never leaves the transponder chip, making the authentication theoretically secure against passive eavesdropping. For a deeper look at the seed-key algorithm extraction process, see our Seed-to-Key Reverse Engineering guide.
Immobilizer Generations: From Fixed Code to AES-128
ECU immobilizer technology has evolved significantly over three decades. Each generation introduced stronger cryptographic protections, and understanding these generations is critical for choosing the correct reverse engineering approach.
| Generation | Era | Crypto Type | Key Length | RE Difficulty |
|---|---|---|---|---|
| IMMO1 / EWS1 | 1994-1997 | Fixed code | 32-bit | Low |
| IMMO2 / EWS2 | 1997-2000 | Rolling code | 32-bit | Low-Medium |
| IMMO3 / EWS3 | 2000-2005 | Challenge-response (Megamos, DST40) | 40-48 bit | Medium |
| IMMO4 / CAS2-3 | 2005-2012 | Challenge-response (Hitag2, DST80) | 48-80 bit | Medium-High |
| IMMO5+ / FEM/BDC | 2012-present | AES-128, bilateral auth | 128 bit | High |
VAG Immobilizer Generations (VW, Audi, Skoda, SEAT)
Volkswagen Group vehicles use a well-documented immobilizer progression. IMMO1 systems (1994-1997) stored a fixed transponder code that could be read directly from the instrument cluster EEPROM. IMMO2 introduced rolling codes synchronized between the cluster and ECU. IMMO3 added a separate immobilizer module with challenge-response authentication using the Megamos crypto transponder. IMMO4 and IMMO5 moved to Component Protection with online server authentication, making offline ECU immobilizer bypass significantly more complex.
BMW EWS and CAS Architecture
BMW uses a unique immobilizer architecture that evolved from EWS (Elektronische Wegfahrsperre) to CAS (Car Access System). The EWS module communicates with the DME/DDE (engine ECU) through an ISN (Individual Serial Number) that must match between both modules. EWS2 used a static ISN, while EWS3 introduced a “rolling ISN” that changes with every successful engine start. CAS modules (CAS1 through CAS4) integrated more vehicle functions and introduced stronger encryption. The transition from EWS to CAS is particularly relevant for ECU immobilizer reverse engineering because the ISN storage location and encryption method differ between each version.
Other OEM Systems
Toyota uses a transponder key ECU that communicates with the engine ECU and instrument cluster simultaneously. Mercedes-Benz integrates its immobilizer into the EIS (Electronic Ignition Switch) and ESL (Electronic Steering Lock) modules. Bosch-based implementations on MED17 and EDC17 platforms use Tricore-specific security routines embedded deep in the firmware. For detailed analysis of these Bosch platforms, see our Bosch MED17 and EDC17 Reverse Engineering Guide.
Need help with an ECU immobilizer project? Whether you are dealing with a corrupted ISN, a locked ECU after replacement, or a forensic investigation requiring immobilizer data extraction, our team has hands-on experience across all major OEM platforms. Learn about our ECU reverse engineering services.
EEPROM Data Structure: Where Immobilizer Secrets Live
The EEPROM (Electrically Erasable Programmable Read-Only Memory) is the non-volatile storage chip inside the ECU that holds immobilizer-critical data. Understanding the EEPROM layout is the foundation of any ECU immobilizer reverse engineering effort.
What the EEPROM Stores
A typical immobilizer EEPROM contains the following data blocks:
- VIN (Vehicle Identification Number): Links the ECU to a specific vehicle. Usually stored in plaintext or with simple XOR encoding.
- ISN (Individual Serial Number): The cryptographic key that pairs the ECU to the immobilizer module. This is the most critical value for reverse engineering work.
- Transponder key slots: Storage for 4-8 registered key IDs and their associated cryptographic data.
- Synchronization counters: Rolling code counters that must match between the ECU and the immobilizer module.
- Immobilizer status flags: Bytes indicating whether the system is active, virgin (unprogrammed), or in service mode.
- Calibration checksums: Integrity values protecting the EEPROM content from unauthorized modification.
Common EEPROM Chips in Immobilizer Systems
| Chip | Size | Common In | Read Method |
|---|---|---|---|
| 93C56 (IC900) | 256 bytes | Toyota, Lexus, older Bosch | In-circuit or desoldered |
| 93C66 | 512 bytes | Honda, Subaru | In-circuit |
| 93C76 / 93C86 | 1-2 KB | Bosch ME7, EDC15 | In-circuit or desoldered |
| 24C02 / 24C04 | 256-512 bytes | Siemens/Continental, Marelli | I2C in-circuit |
| Internal D-Flash | Variable | Bosch MED17/EDC17 (Tricore) | JTAG, Boot Mode, BDM |
On older ECUs, the EEPROM is a separate physical chip that can be read with a clip programmer without desoldering. On modern Bosch MED17 and EDC17 platforms, the immobilizer data is stored in the Tricore microcontroller’s internal data flash (D-Flash), which requires more advanced extraction methods. For a complete comparison of these techniques, refer to our ECU Firmware Extraction Methods guide.
ISN Recovery: The Core of ECU Immobilizer Reverse Engineering
ISN stands for Individual Serial Number, and it is the single most important value in immobilizer security. The ISN is a cryptographic pairing code that links the engine ECU to the vehicle’s immobilizer module. Without a matching ISN on both sides, the engine will not start, regardless of whether the correct transponder key is present.
Why ISN Recovery Matters
ISN recovery becomes necessary in several real-world scenarios:
- ECU replacement: When a faulty ECU is replaced with a used or new unit, the ISN in the replacement will not match the vehicle’s immobilizer module. The new unit must either receive the original ISN, or the immobilizer module must be updated with the new ISN.
- Lost key situations: If all transponder keys are lost, recovering the ISN from the ECU allows a locksmith or technician to program new keys without replacing hardware.
- Forensic investigation: In vehicle theft analysis or insurance fraud cases, ISN data provides evidence of whether the immobilizer was tampered with.
- Module cloning: Creating a plug-and-play replacement ECU requires extracting and transferring the complete ISN and immobilizer dataset.
ISN Recovery Methods
The approach to ISN recovery depends on the ECU immobilizer generation and the specific hardware platform:
1. Direct EEPROM read: On older ECUs with external EEPROM chips (93C56, 93C66, 93C76), the ISN can be read directly using a SOIC clip programmer. The ISN location within the EEPROM is typically documented for common ECU types. This is the simplest approach and works reliably on IMMO1 and IMMO2 systems.
2. OBD diagnostic extraction: Some platforms allow ISN readout through the OBD-II diagnostic port using specialized tools like Autohex, AVDI, or FVDI. This method relies on exploiting the UDS (Unified Diagnostic Services) SecurityAccess service. The tool sends a seed-key authentication sequence to unlock the ECU, then reads the ISN from a protected memory area.
3. Boot mode extraction: On Tricore-based Bosch ECUs (MED17, EDC17), the ISN is stored in the internal D-Flash. Accessing it requires putting the microcontroller into boot mode and reading the flash content using a BSL (Bootstrap Loader) protocol. This method requires opening the ECU and connecting directly to the Tricore processor’s boot pins.
4. JTAG/BDM extraction: For ECUs with active debug interfaces, JTAG or BDM connections provide full memory access, including the ISN storage area. This is the most thorough extraction method because it allows reading the entire flash and RAM content, not just the EEPROM region.
5. Firmware reverse engineering: When the ISN is encrypted or stored in a non-standard location, static analysis of the firmware using tools like Ghidra or IDA Pro can reveal the ISN storage format, encryption algorithm, and memory address. This is the most advanced form of ECU immobilizer reverse engineering and requires significant expertise in embedded systems analysis. Our Advanced ECU Firmware Reverse Engineering Methodology covers this process in detail.
Struggling with ISN recovery on a specific platform? We have successfully recovered ISN data from Bosch, Siemens/Continental, Denso, Delphi, and Marelli ECUs across hundreds of vehicle models. Contact us for a free consultation.
ECU Virginization: Resetting the Immobilizer State
ECU virginization is the process of resetting an engine control unit’s immobilizer data to its factory-unprogrammed state. A “virgin” ECU behaves as if it has never been installed in a vehicle, meaning it has no stored ISN, no registered transponder keys, and no VIN association. This allows the unit to be paired with any compatible immobilizer module during a fresh key learning procedure.
When Virginization Is Used
Immobilizer virginization serves several legitimate purposes. Automotive recyclers virginize used ECUs to create affordable replacement parts. Repair shops virginize units when the original immobilizer module has been destroyed and a complete system reset is the only option. Security researchers use virginization to study the pairing process from a clean starting state.
Virginization Methods by Platform
| ECU Platform | Virginization Method | Complexity | Notes |
|---|---|---|---|
| Bosch ME7, EDC15 | EEPROM overwrite with virgin dump | Low | External 93C76 chip, well documented |
| Bosch MED17, EDC17 | D-Flash modification via boot mode | High | Internal flash, encrypted ISN on newer variants |
| Siemens/Continental SIMOS | EEPROM reset via diagnostic tool | Medium | Requires SecurityAccess unlock first |
| Denso (Toyota, Subaru) | 93C56 EEPROM overwrite | Low-Medium | IC900 position, virgin dumps available |
| BMW DME (EWS era) | ISN clear via EWS alignment tool | Medium | EWS module must also be reset |
| BMW DME (CAS era) | ISN write via ISTA+ or Autohex | High | Some CAS3+ have OTP ISN (non-resettable) |
A critical consideration for virginization is checksum integrity. After modifying EEPROM data, the internal checksums must be recalculated, or the ECU will detect the modification and enter a fault state. Our ECU Checksum and CRC Algorithms guide covers checksum correction techniques in depth.
ECU Cloning: Full Immobilizer Data Transfer
ECU cloning is a step beyond virginization. Instead of resetting the immobilizer to a blank state, cloning transfers the complete identity of one ECU to another. The cloned unit becomes a plug-and-play replacement that works with the vehicle’s existing keys and immobilizer module without any reprogramming.
What Gets Cloned
A proper clone operation transfers:
- Complete EEPROM content (VIN, ISN, key data, counters, calibration)
- Flash memory software version (must match or be compatible)
- Hardware-specific adaptations and coding data
- Immobilizer synchronization state
The Encryption Challenge
On modern ECUs, particularly Bosch MED17 and EDC17 platforms, simply copying the raw EEPROM data from one unit to another does not produce a working clone. The immobilizer data in the EEPROM is often encrypted using a key derived from the flash memory content or the microcontroller’s unique hardware ID. This means the encrypted EEPROM data is only valid for the specific chip it was encrypted on.
Successful cloning requires decrypting the EEPROM data from the source ECU, then re-encrypting it using the destination unit’s hardware-specific key. This is one of the most technically demanding tasks in ECU immobilizer reverse engineering and requires detailed knowledge of the encryption algorithm used by each variant.
Tools and Hardware for Immobilizer Reverse Engineering
Working with ECU immobilizer systems requires both specialized hardware and software. The following table summarizes the essential tools used by professionals in this field.
| Category | Tool | Primary Use |
|---|---|---|
| EEPROM Programmer | XPROG, Orange5, UPA-USB | Reading and writing external EEPROM chips for immobilizer data |
| Diagnostic Interface | Autohex II, AVDI (Abrites), FVDI | OBD-based ISN read/write, key programming, immobilizer alignment |
| ECU Flasher | Kess V2, KTag, CMD Flash | Boot mode and bench mode flash reading for Tricore platforms |
| Debug Probe | Lauterbach TRACE32, PLS UDE, J-Link | JTAG/BDM/SWD access for full memory dump including immobilizer regions |
| Disassembler | Ghidra, IDA Pro, Binary Ninja | Static analysis of firmware routines and immobilizer algorithms |
| Hex Editor | HxD, WinOLS, 010 Editor | EEPROM data inspection and manual byte manipulation |
| Cloning Platform | HexProg, HexTag, SmartSafe | Automated ECU cloning with built-in immobilizer data migration |
The choice of tooling depends heavily on the immobilizer generation. Older systems with external EEPROM chips can be handled with a $50 clip programmer. Modern Tricore-based systems may require a professional bench setup costing several thousand dollars, combined with custom scripts and deep firmware analysis expertise.
Security Considerations and Modern Defenses
As ECU immobilizer reverse engineering techniques have advanced, so have the countermeasures implemented by OEMs and ECU manufacturers. Understanding these defenses is essential for any serious reverse engineering effort.
OTP (One-Time Programmable) Memory
Some modern ECUs store the ISN in OTP memory regions that can only be written once. Once programmed, the ISN cannot be changed, making the ECU permanently married to a specific vehicle. This is one of the strongest immobilizer protections because it eliminates the possibility of ISN modification through software alone. Physical chip replacement or microcontroller swapping becomes the only option.
Encrypted EEPROM Content
Newer Bosch MED17 variants encrypt the entire EEPROM content using a key derived from the microcontroller’s unique silicon ID. Even if the EEPROM is successfully read, the immobilizer data appears as meaningless encrypted bytes without knowledge of the decryption algorithm and the hardware-specific key.
Server-Side Authentication
The latest immobilizer systems (VAG IMMO5+, BMW FEM/BDC with latest firmware) require online server authentication for key programming and ISN matching. The vehicle connects to the manufacturer’s server, which verifies ownership and authorization before releasing the cryptographic tokens needed to complete the procedure. This effectively moves the security boundary from the vehicle to the OEM‘s cloud infrastructure.
Bilateral Authentication
In the most advanced systems, the immobilizer protocol uses bilateral (mutual) authentication. Not only does the ECU verify the key, but the key also verifies the ECU. This prevents attacks where a cloned module accepts unauthorized keys. AES-128 with rolling session keys provides the cryptographic backbone for these systems.
ECU Immobilizer Reverse Engineering Workflow
A professional engagement follows a structured methodology. Here is the typical workflow from initial assessment to final delivery:
Step 1: Identification and Research
Identify the exact ECU hardware number, software version, and the immobilizer generation. Cross-reference the part number with known EEPROM locations and ISN formats. Determine which extraction method is appropriate for this specific platform.
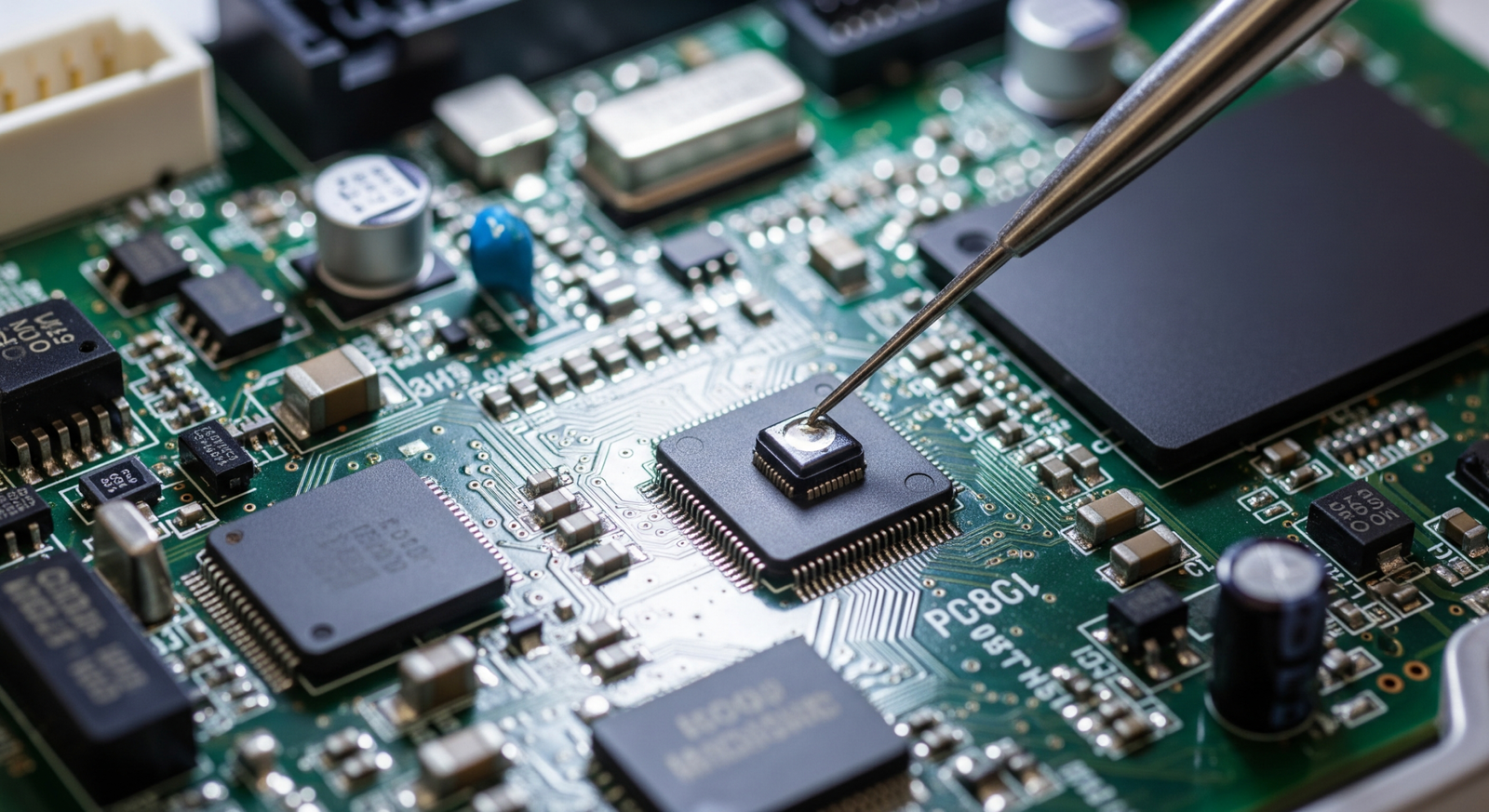
Step 2: Hardware Access and Extraction
Open the ECU enclosure and identify the EEPROM chip or flash memory. Read the full memory content using the appropriate method: clip programmer for external EEPROMs, boot mode for Tricore D-Flash, or JTAG/BDM for full memory dumps. Always create a verified backup before any modification.
Step 3: Data Analysis and ISN Location
Load the extracted data into a hex editor and locate the immobilizer data blocks. Use known patterns, offset tables, and binary comparison with reference dumps to identify the ISN, key slots, VIN, and synchronization counters. For unknown ECU types, static firmware analysis using Ghidra helps identify the immobilizer routines and their data references.
Step 4: Modification or Recovery
Depending on the objective, either extract the ISN for transfer to a replacement ECU, or modify the EEPROM data to achieve virginization or cloning. Apply the necessary checksum corrections to ensure the ECU accepts the modified data without errors.
Step 5: Verification and Testing
Flash the modified data back to the ECU. Test the immobilizer function on a bench setup before vehicle installation. Verify that key learning, engine start authorization, and all immobilizer-related diagnostic codes function correctly.
This workflow applies across all platforms, with variations in the specific tools and techniques used at each step. The Bosch ECU family, which covers a large portion of the European vehicle market, follows this general pattern with platform-specific details. For an overview of Bosch platforms and their characteristics, see our Bosch ECU Tuning and Reverse Engineering Overview.
Real-World Applications
ECU immobilizer reverse engineering is not just an academic exercise. It solves real problems for vehicle owners, repair shops, forensic investigators, and security researchers every day.
Automotive repair and ECU replacement: When a vehicle’s original ECU fails, the replacement unit must be paired with the existing immobilizer system. Dealer-level tools can handle this for newer vehicles under warranty, but for older vehicles, aftermarket ECUs, or situations where dealer access is unavailable, immobilizer reverse engineering provides the only path to a working repair.
Vehicle forensics and theft investigation: Law enforcement and insurance investigators use immobilizer analysis to determine whether a vehicle was stolen using electronic bypass methods. The presence of modified EEPROM data, cleared ISN values, or aftermarket emulators provides critical evidence in these investigations.
Automotive security research: Academic researchers and security consultants study immobilizer implementations to identify vulnerabilities and recommend improvements. Published research on Megamos, Hitag2, and DST40 transponder weaknesses has driven the industry toward stronger AES-based solutions.
Key programming and locksmith services: Professional locksmiths rely on immobilizer knowledge to program replacement keys when all original keys are lost. Understanding the ISN recovery process and the key learning protocol is essential for this work.
ECU immobilizer reverse engineering is one of the most technically demanding disciplines in automotive security. From early fixed-code transponders to modern AES-128 bilateral authentication systems, the complexity has increased dramatically with each generation. Success in this field requires a combination of hardware skills (EEPROM reading, soldering, bench setup), software expertise (firmware disassembly, cryptographic analysis), and deep platform-specific knowledge of how each OEM implements its immobilizer architecture.
The key takeaways from this guide are clear. First, always identify the exact immobilizer generation before selecting your approach. Second, the ISN is the central piece of the puzzle, and its recovery method varies significantly between platforms. Third, modern systems with OTP memory, encrypted EEPROMs, and server-side authentication require increasingly sophisticated techniques. And fourth, proper checksum correction after any EEPROM modification is non-negotiable.
Whether you are a repair technician facing an ECU replacement challenge, a forensic investigator analyzing vehicle security, or a researcher studying automotive cryptography, understanding ECU immobilizer internals gives you the foundation to tackle any immobilizer-related problem with confidence.
Let's Work Together
Need Professional Assistance with Reverse Engineering or Cybersecurity Solutions? Our Team is Ready To Help You Tackle Complex Technical Challenges.