Ever Needed to Reverse Engineer a Hardware Device? Here’s How We Do It.
Hardware is everywhere—from industrial machines and automotive systems to IoT devices, routers, and security chips. But what happens when you need to extract data, analyze firmware, modify circuits, or bypass security mechanisms?
Many devices are locked behind encryption, secure boot protections, or proprietary chips—making them nearly impossible to modify without proper reverse engineering techniques.
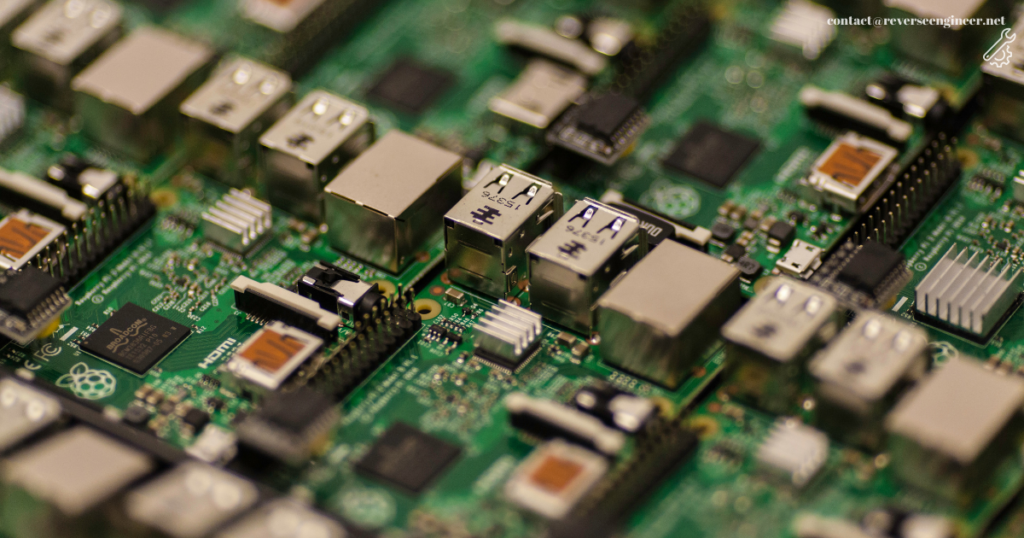
At ReverseEngineer.net, we specialize in hardware reverse engineering, chip-level analysis, and PCB modifications to help you unlock, analyze, and optimize embedded systems.
Why Do People Need Hardware Reverse Engineering?
Hardware isn’t always designed for flexibility. You might need to:
🔹 Extract firmware from a secure microcontroller for analysis or modification.
🔹 Bypass hardware protections like JTAG locks, EEPROM encryption, or Secure Boot.
🔹 Analyze printed circuit boards (PCBs) to replicate or modify their design.
🔹 Recover data from damaged or unsupported hardware.
🔹 Identify vulnerabilities in hardware security chips.
The challenge? Manufacturers implement advanced hardware protections to prevent tampering.
🚀 Need professional hardware reverse engineering? Contact us now!
How We Reverse Engineer Hardware: A Real-World Example
A client approached us with a proprietary industrial controller used in a manufacturing system. The company that built it was no longer in business, and they needed access to the firmware to integrate it with new equipment.
Here’s how we handled it:
🔍 Step 1: Identifying the Hardware & Extracting the Firmware
We first examined the hardware, identifying key components such as:
✔ Microcontroller & memory chips (EEPROM, NAND, NOR Flash)
✔ JTAG & UART debugging interfaces
✔ Encrypted bootloaders & security fuses
Using SPI flash dumping and JTAG debugging, we successfully extracted the firmware for further analysis.
🛠 Step 2: Analyzing & Modifying the Firmware
We decompiled the firmware using IDA Pro, Ghidra, and Binwalk, revealing:
✔ Hidden security features preventing unauthorized access.
✔ Configuration settings locked behind encrypted storage.
✔ API endpoints communicating with other factory machines.
We then patched the firmware, allowing it to work with modern systems.
🗃 Step 3: Testing & Restoring Full Functionality
After flashing the modified firmware back to the hardware, we ensured:
✅ The controller functioned without manufacturer restrictions.
✅ New equipment could communicate with the device seamlessly.
✅ The system was fully operational—without requiring outdated dependencies.
🚀 Need something similar? Talk to us!
How Hardware is Protected (And How We Overcome It)
Manufacturers use a variety of hardware-level security mechanisms to prevent reverse engineering. These include:
🔐 JTAG & UART Security Protections
- JTAG Locking – Disables debugging access.
- UART Authentication – Prevents serial communication with the device.
💡 We bypass JTAG & UART locks using advanced debugging and hardware exploit techniques.
🛡 Secure Boot & Encrypted Firmware Protections
- AES-Encrypted Firmware – Prevents unauthorized modifications.
- Secure Bootloaders – Ensures only signed firmware can be executed.
💡 We analyze and extract firmware even when encrypted with AES/RSA-based protections.
🔗 Chip-Level Security Implementations (EEPROM, SPI, NAND/NOR Flash Encryption)
- EEPROM Data Locking – Prevents direct memory reads.
- Flash Memory Readout Protection (RDP) – Stops firmware dumping.
💡 Using hardware probing & side-channel analysis, we extract encrypted firmware for analysis.
Success Stories: Real Clients, Real Solutions
1️⃣ Extracting Encrypted Firmware from a Locked Microcontroller
A company needed access to firmware stored inside a locked STM32 microcontroller, but the chip’s readout protection (RDP) prevented dumping.
✅ Using fault injection and side-channel analysis, we successfully extracted the firmware.
2️⃣ Reverse Engineering a Proprietary PCB for Replication
A client needed to duplicate a discontinued PCB, but there was no documentation available.
✅ We reverse-engineered the PCB, traced its circuits, and recreated a working design.
🚀 Need hardware reversed or modified? Talk to us!
FAQs: Everything You Need to Know About Hardware Reverse Engineering
1️⃣ Is hardware reverse engineering legal?
Yes! Reverse engineering is legal for research, security analysis, and interoperability purposes. However, modifying proprietary hardware without authorization may violate licensing agreements.
2️⃣ Can you extract firmware from a protected microcontroller?
Yes! We specialize in:
✔ JTAG & UART debugging
✔ EEPROM & SPI flash dumping
✔ Secure Boot & encryption bypass
3️⃣ Can you reverse engineer a PCB?
Absolutely! We can:
✔ Trace & replicate PCB designs
✔ Analyze proprietary circuits
✔ Extract component data & schematics
Need Hardware Reverse Engineering? Contact Us Today!
At ReverseEngineer.net, we provide:
✔ Microcontroller & chip-level analysis
✔ JTAG & UART hardware debugging
✔ EEPROM & SPI firmware extraction
✔ Reverse engineering of custom PCBs & circuits
📌 Visit: reverseengineer.net
📩 Email us: [email protected]
🚀 Need hardware reversed? Let’s talk!
Let's Work Together
Need Professional Assistance with Reverse Engineering or Cybersecurity Solutions? Our Team is Ready To Help You Tackle Complex Technical Challenges.