
Why TriCore Dominates Automotive ECU Design
The Infineon TriCore processor is the most widely used microcontroller architecture in automotive engine management. From Bosch MED17 and EDC17 units to Continental Simos and Valeo VD56 platforms, TriCore silicon sits at the heart of millions of vehicles worldwide. For anyone working in ECU reverse engineering, understanding TriCore architecture is not optional. It is the foundation that every other skill builds upon.
At ReverseEngineer.net, TriCore is our most frequently encountered architecture. We analyze TriCore-based firmware across all major ECU manufacturers, and this deep familiarity with the silicon itself is what enables efficient, accurate reverse engineering results. This article explains why TriCore dominates automotive ECU design and what makes this architecture unique from a reverse engineering perspective.
TriCore Architecture Overview: Three in One
The name “TriCore” reflects the processor’s three-core design philosophy. It combines a RISC processor core for general computation, a microcontroller core for real-time interrupt handling, and a DSP core for signal processing, all in a single unified pipeline. This tri-functional design eliminates the need for separate processors, reducing cost and board complexity while delivering the performance that modern engine management demands.
For reverse engineers, this unified architecture means that a single firmware binary contains all three types of code: general application logic, interrupt-driven real-time control, and DSP-style signal processing algorithms. Recognizing which sections of code serve which purpose is key to efficient TriCore ECU analysis.
Key TriCore Variants in Automotive ECUs
| TriCore Variant | Generation | Clock Speed | Common ECUs |
|---|---|---|---|
| TC1766 / TC1767 | TC1.3 | 150 MHz | Bosch MED17.1, Continental Simos 8/10 |
| TC1797 | TC1.6P | 180 MHz | Bosch MED17.5, EDC17C46, Continental Simos 12 |
| TC275 / TC277 | AURIX TC2xx | 200 MHz | Bosch MD1/MG1, Continental Simos 16/18 |
| TC298 | AURIX TC2xx | 200 MHz | Bosch MD1CP014, Continental Simos 18.x |
| TC375 / TC377 | AURIX TC3xx | 300 MHz | Continental Simos 19, Bosch MD1CE100 |
| TC397 | AURIX TC3xx | 300 MHz | Next-gen powertrain ECUs, ADAS controllers |
Each generation brings higher clock speeds, more flash memory, additional CPU cores, and stronger security features. For a detailed look at how specific TriCore ECUs are structured, see our Bosch MED17 and EDC17 Reverse Engineering Guide.
TriCore Memory Architecture
Understanding the TriCore memory map is essential for loading firmware correctly into analysis tools and for interpreting address references in disassembled code. The architecture uses a segmented memory model with distinct regions for program flash, data flash, RAM, and peripheral registers.
| Address Range | Region | Purpose |
|---|---|---|
| 0x80000000 – 0x80FFFFFF | PFlash (non-cached) | Program flash, direct access |
| 0xA0000000 – 0xA0FFFFFF | PFlash (cached) | Same physical flash, instruction cache enabled |
| 0xAFE00000 – 0xAFEFFFFF | DFlash | Data flash (EEPROM emulation, adaptation values) |
| 0xC0000000 – 0xC000FFFF | PSPR | Program Scratch-Pad RAM (fast, local) |
| 0xD0000000 – 0xD000FFFF | DSPR | Data Scratch-Pad RAM (fast, local) |
| 0x60000000 – 0x6FFFFFFF | Global RAM (AURIX) | LMU/EMEM shared memory on multi-core variants |
| 0xF0000000 – 0xFFFFFFFF | Peripheral Space | CAN, SPI, ADC, timers, SCU, FCE registers |
A common mistake during ECU firmware analysis is loading the binary at the wrong base address. TriCore firmware extracted from PFlash must be loaded at 0xA0000000 (cached) or 0x80000000 (non-cached) for address references to resolve correctly. We cover the practical setup for this in our Ghidra for Automotive ECU Analysis guide.

TriCore Instruction Set: What Reverse Engineers Need to Know
The TriCore instruction set uses a mix of 16-bit and 32-bit instructions, with the lowest bit of the opcode byte determining the instruction length. This variable-length encoding provides good code density, which matters when fitting complex engine management software into limited flash memory.
Register architecture: TriCore provides 16 data registers (d0-d15), 16 address registers (a0-a15), and a Program Counter (PC). Address registers are used for pointer operations and addressing modes, while data registers handle arithmetic and logic. Register pairs (e.g., e0 = d0:d1) support 64-bit operations used in precision calculations for fuel injection timing and ignition control.
Context switching: TriCore implements hardware-assisted context saving through upper and lower context save areas (CSA). When a function call or interrupt occurs, the processor automatically saves registers to a linked list of CSA blocks in RAM. This mechanism is central to the real-time interrupt performance that automotive applications demand, and understanding it is important when tracing call chains in disassembled code.
Circular addressing: The DSP-oriented portion of the instruction set includes circular buffer addressing modes, saturating arithmetic, and packed data operations. These features appear in sensor signal filtering routines and feedback control loops within ECU firmware.
Boot Mode Header and Startup Sequence
Every TriCore-based ECU begins execution through the Boot Mode Header (BMH) mechanism. The BMH is a data structure at a fixed flash address that tells the processor where to start executing code after reset.
For TC1797, the primary BMH (BMHD0) is located at 0xA0000000. It contains the start address (STAD), a CRC for header validation, and configuration flags. The processor reads this header, verifies the CRC, and jumps to the specified start address to begin firmware execution.
The BMH CRC is computed by the TriCore hardware using a specific polynomial. This is separate from any application-level checksum that protects the main firmware code and calibration data. When performing firmware extraction, both the BMH and the application firmware must be captured to produce a complete, bootable image.
AURIX Multi-Core Architecture
The AURIX generation (TC2xx and TC3xx) introduced multi-core processing to automotive ECUs. The TC277, for example, has three TriCore CPUs (CPU0, CPU1, CPU2), each with its own local PSPR and DSPR memory. This multi-core design appears in both Bosch MD1/MG1 and Continental Simos 18/19 platforms.
From a reverse engineering perspective, multi-core firmware presents specific challenges. Different cores execute different parts of the application: Core 0 typically runs the RTOS and diagnostic stack, Core 1 handles the main engine control algorithms, and Core 2 manages auxiliary functions. The firmware binary contains code for all cores, and the startup sequence assigns code regions to each CPU. Our team routinely analyzes multi-core AURIX firmware, mapping the inter-core communication mechanisms and identifying which core owns each critical function.
Working with TriCore-based ECU firmware? Our team has deep experience across TC1767, TC1797, TC275, TC277, TC298, and TC3xx platforms. Learn about our ECU reverse engineering services.
TriCore Security Features
Each TriCore generation has introduced stronger security mechanisms, progressively raising the bar for firmware access and analysis.
Debug port protection (TC1.3/TC1.6): Older TriCore variants use a password-based debug lock. The Device Security Management (DSCM) module requires a correct password to enable JTAG access. If the password is unknown, debug access is blocked. However, the password is stored in flash and can sometimes be recovered through alternative read methods.
Hardware Security Module (AURIX TC2xx): The AURIX HSM is a dedicated security processor with its own flash, RAM, and cryptographic accelerators. It implements secure boot, key storage, and seed-key authentication independently from the main TriCore CPUs. Even if the main firmware is fully compromised, HSM-protected keys remain inaccessible through normal analysis methods.
Secure Boot (AURIX TC3xx): The latest generation adds hardware-rooted secure boot that verifies firmware integrity using asymmetric cryptography before execution. Combined with encrypted flash regions and secure debug authentication, TC3xx represents the most challenging TriCore platform for reverse engineering.
Understanding these security layers is essential for planning any TriCore ECU analysis project. The approach that works on a TC1797-based MED17 will not work on a TC377-based Simos 19 without adapting to the additional security mechanisms.
TriCore Peripherals Relevant to ECU Analysis
TriCore integrates numerous peripherals that are critical for ECU functionality. Recognizing peripheral register accesses in disassembled code accelerates firmware understanding.
MultiCAN/CAN-FD: The CAN controller handles all vehicle network communication. Identifying CAN register accesses leads to the diagnostic handler (UDS), CAN message processing, and calibration download routines.
GTM (Generic Timer Module): The GTM drives fuel injection timing, ignition coil control, and PWM outputs. It is the most complex TriCore peripheral, with hundreds of configuration registers. GTM-related code typically contains the most performance-critical engine control algorithms.
VADC (Versatile ADC): Analog-to-digital conversion for all sensor inputs: throttle position, manifold pressure, exhaust gas temperature, knock sensors. ADC initialization code reveals which physical pins connect to which sensor channels.
FCE (Flexible CRC Engine): Hardware CRC computation used for firmware integrity verification, checksum validation, and communication integrity checks. The FCE configuration (polynomial, initial value) determines the CRC algorithm used by the ECU.
DMU/PMU (Data/Program Memory Units): Flash programming is controlled through these modules. Understanding DMU register sequences is necessary for analyzing bootloader flash routines and immobilizer data storage mechanisms.
Need TriCore ECU firmware analyzed? From first-generation TC1767 to latest AURIX TC3xx, our team delivers comprehensive reverse engineering results. Get in touch to discuss your project.
TriCore in Ghidra: Practical Analysis Notes
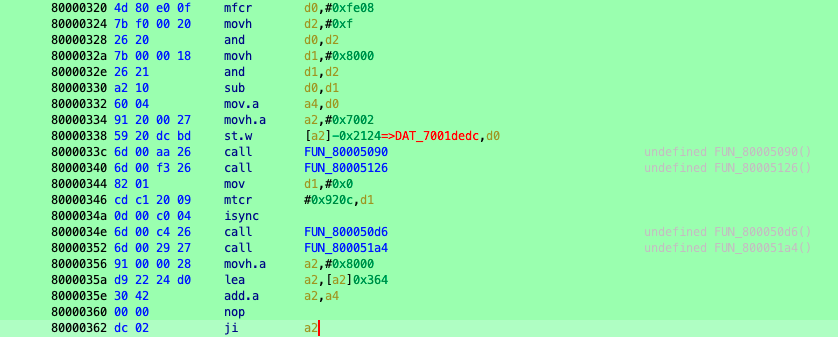
Ghidra’s built-in TriCore support makes it the preferred analysis platform for automotive ECU firmware. A few practical notes from our extensive TriCore analysis experience:
Processor selection matters. Ghidra offers multiple TriCore variants (default, TC172x, TC176x, TC29x). Selecting the correct variant ensures accurate instruction decoding, especially for AURIX-specific instructions not present in older cores.
Base address is critical. Always load PFlash dumps at 0xA0000000. Function calls, data references, and jump tables use absolute addresses in the 0xA0xxxxxx range. Loading at 0x00000000 leaves thousands of cross-references unresolved.
Register labeling transforms readability. TriCore peripheral registers at 0xF0xxxxxx appear as raw memory accesses in decompiled code. Applying register labels from the Infineon datasheet (e.g., labeling 0xF0036100 as “SCU_WDTCPU0_SR”) makes the code immediately understandable. Automated scripts for this are part of our standard analysis methodology.
CSA analysis for call tracing. The hardware context save mechanism means that standard stack-based call analysis does not always apply. Understanding CSA linked lists is necessary for accurate call graph reconstruction in complex firmware.
The Infineon TriCore architecture is the dominant force in automotive ECU design, and its presence is only growing with each new vehicle generation. From the single-core TC1767 in legacy Bosch MED17 units to the six-core TC397 in next-generation powertrain controllers, TriCore knowledge is the single most valuable skill for anyone working in automotive ECU reverse engineering.
The architecture’s combination of real-time performance, integrated peripherals, and evolving security features makes it both powerful and challenging to analyze. Each TriCore generation requires updated knowledge and adapted techniques. At ReverseEngineer.net, we maintain current expertise across all TriCore generations, ensuring we can deliver results regardless of which specific variant powers the target ECU.
Let's Work Together
Need Professional Assistance with Reverse Engineering or Cybersecurity Solutions? Our Team is Ready To Help You Tackle Complex Technical Challenges.